MQTT Gateway – Wi-Fi Micro Gateway for MQTT
Highlights
- MQTT Gateway for Connection to NCD IoT Sensors
- Plug-and-Play Setup Requires Only Wi-Fi and MQTT Login Credentials
- SoftAP Web-Page Configuration of Gateway and MQTT Settings
- Up to 2-Mile Wireless Range Between IoT Sensors and Gateway
- Up to 10 Meter Wireless Range Between Gateway and Wi-Fi Router
- Encrypted Communications Between IoT Sensors and Gateway
- Encrypted Communications Between Gateway and Wi-Fi Connection
- Encrypted Communications Between Gateway and MQTT
- Automatically Discovers IoT Sensors & Report to MQTT with Zero Setup
- Integrated Web-Page Allows Configuration of Remote IoT Sensors
- Integrated Web-Page Displays Incoming IoT Sensor Data
- Supports DHCP or Static IP Managed Wireless Networks
- Automatically Registers Sensors and Pushes Sensor Data to MQTT
- Compatible with All NCD Wireless IoT Sensors
- Allows Multiple Gateways to Co-Exist for Redundant Data
- Over the Air Firmware Update Support Coming Soon
- NOT RECOMMENDED FOR NEW DESIGN
- Click here for Direct Replacement
IoT Sensors need a MQTT Gateway. MQTT is the foundation for nearly all IoT cloud applications, so building a MQTT Gateway for connection to the NCD ecosystem of IoT sensors was an absolute requirement.
The NCD Wi-Fi Micro Gateway connects NCD Wireless IoT Sensors directly to a MQTT broker with an average setup time of about 5 minutes. The NCD Wi-Fi Micro Gateway listens for sensor data from NCD Wireless IoT Sensors up to 2 miles away and converts the incoming data into JSON strings with real-world human-readable values. Use the MQTT Gateway to quickly and easily measure temperature and post directly to your own MQTT broker. Send humidity data, current measurements for power consumption, light level data, counter data, and much more. The NCD Micro Gateway is compatible with the entire NCD Enterprise product line of wireless IoT sensors.
Our MQTT Gateway user interface supports up to 10 IoT sensors while in configuration mode, displaying the signal strength and sensor data for each sensor during setup. In Run mode (daily use), the NCD Micro Gateway will work with as many IoT sensors as memory will allow (estimated to be greater than 20, but we did not set a hard limit). The NCD Micro Gateway may also be used for configuration of basic settings of remote wireless IoT sensors.
Ubidots Compatibility
This device has been tested with the Ubidots IoT Cloud Platform for compatibility. Ubidots is an official partner of NCD, and we are working together to connect our entire line of IoT connected hardware to the Ubidots platform. Learn more about Ubidots by clicking here.
What Frequency Do I Need?
Range and Frequency of NCD Wireless Sensors
During purchase, you will see three frequency options. Not all options are legal for use in all areas, so it’s important to make the right selection during purchase. We will build your product and accessories based on the options chosen. Here, we will explain these options in much greater detail, but please check your local laws BEFORE purchase.
900MHz for North America (U.S., Canada, and Mexico)
If you are located in North America, the 900MHz Option will provide the longest range currently supported with the best penetration through walls, buildings, industrial equipment, and trees. This option is also the best choice for long range applications.
900MHz Wireless Sensor Range
The official Line of Sight rating for this option is 2 Miles with included antennas or 28 Miles with high-gain antennas. These distances are characterized for direct line of sight applications with no obstructions. Real-world range will vary greatly depending on surrounding buildings, trees, and other objects that may cause reflections or interfere with the transmission. 900MHz has excellent RF penetration characteristics, and we have successfully completed installations in excess of of a half mile on a automotive factory floor with active robots in between. We have also seen excellent penetration in mild radioactive installations making this a possible candidate for use in nuclear energy applications.
We suggest contacting Digi.com for a high-gain antenna recommendation if required. Please check your local laws before choosing this option.
868MHz for Europe Only

If you are located in Europe, the 868MHz Option is the longest range choice available at this time. This option offers better penetration through walls, buildings, trees, and industrial equipment than 2.4GHz. The official line of site rating for this option is 14.5km using 2.1dBi antennas. Please check your local laws before choosing this option.
2.4Ghz for Worldwide Use
The 2.4GHz option should be chosen if 900MHz and 868MHz are not legal for use in your country. This option is now certified for use worldwide, including Europe, United States, Japan, Australia, Brazil, and South Korea. Please check your local laws before choosing this option just in case 2.4GHz is not legal in your area.
Not Sure?
If you are unsure of which sensor option to choose, please contact us. We may be able to help determine which sensors are legal for use in your area.
MQTT Gateway Configuration Pages
The MQTT Gateway includes a embedded web page configuration screen that makes setup easy, simply register the gateway with your Wi-Fi router by selecting the network name and entering your password, then setup your MQTT login and password:

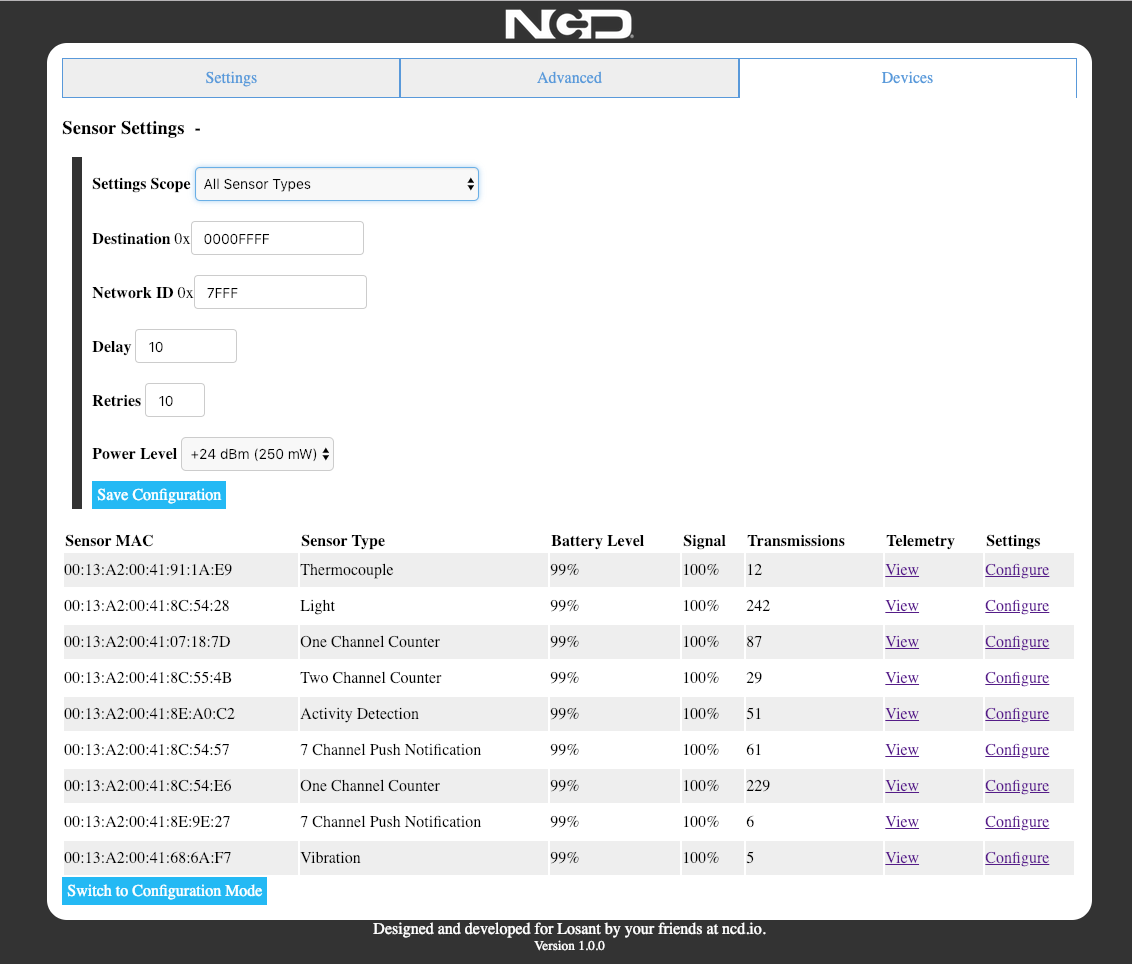 Watch Data Stream In from NCD Wireless Sensors and Review Sensor Readings so you Know your Network is Active!
Watch Data Stream In from NCD Wireless Sensors and Review Sensor Readings so you Know your Network is Active!
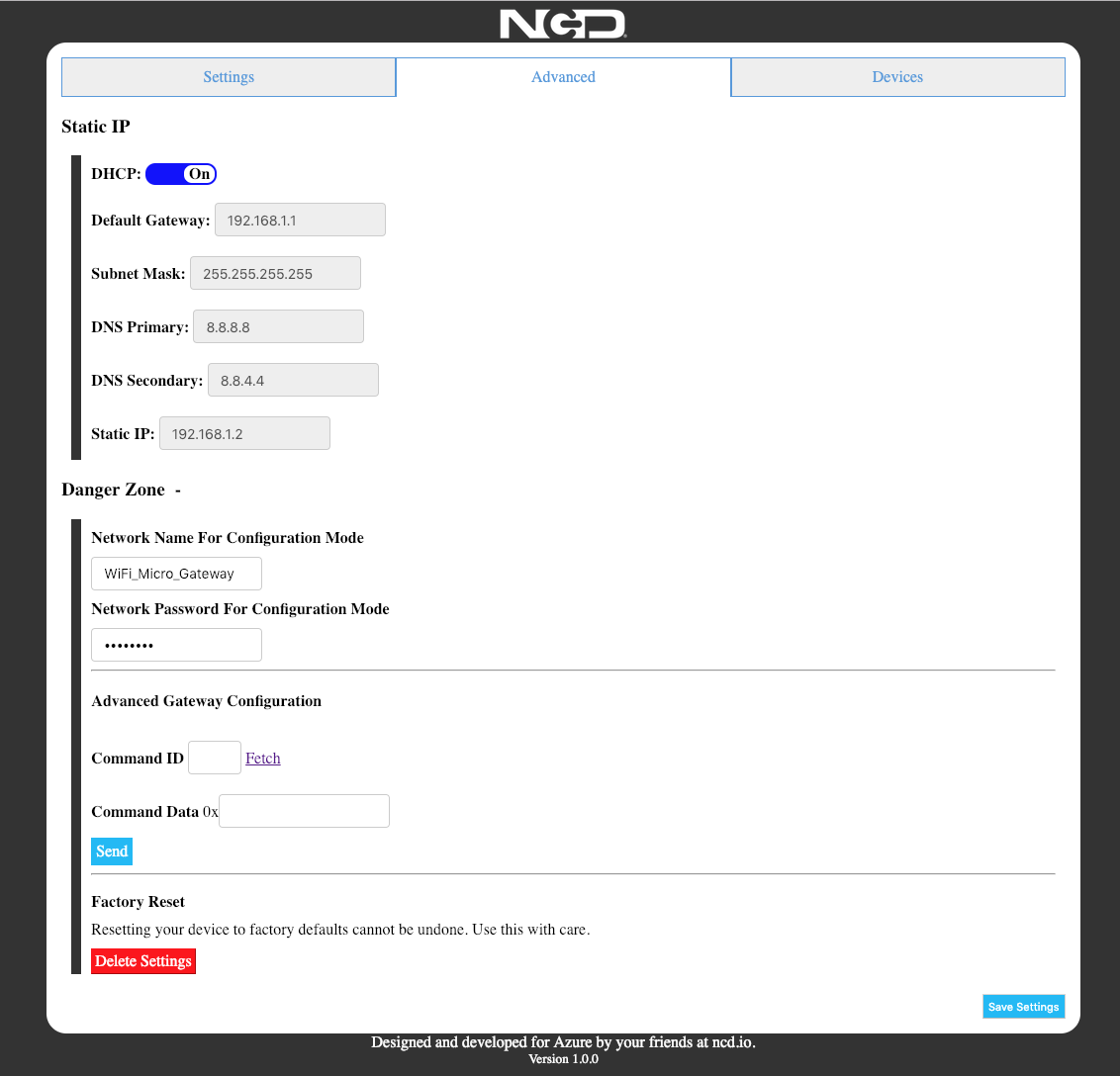 Change Advanced Settings for use with Managed Networks
Change Advanced Settings for use with Managed Networks
IoT Security and Transparency Statement
All IoT Device Manufacturers should commit to IoT Security and Transparency. As a consumer, you have the right to a IoT Security and Transparency Statement BEFORE purchase, and we encourage all customers to demand this information from all IoT Manufacturers and Vendors. In an effort to be fully transparent with our customers, we will always disclose the most important security related information at the bottom of each product page for all IoT Devices. Under no circumstances does NCD use IoT devices to collect customer data, sensor readings, or other information without full disclosure. As a matter of NCD IoT Security Policy, any IoT device that collects any form of data must be disclosed in the IoT Security and Transparency Statement. In the statements below, we will use the term “Wireless” to indicate localized communications between the Sensors and the Gateway. We will use the term “WiFi” to indicate communications between the Gateway and the Internet. Relevant Security Information pertaining to this particular device is Indicated Below:
- This Device Connects to the Internet for the Purposes of Forwarding Wireless AES Encrypted Sensor Data to a 3rd Party Cloud Platform using WiFi Communications
- This Gateway Follows the Security Standards as Defined by the 3rd Party Cloud Platform
- This Gateway Cannot Function Without Following the Security Standards Set Forth by the 3rd Party Cloud Platform
- This Device Utilizes a Write-Only Application Layer, It is Not Possible to Remotely (Over the Internet) Upload Files or Launch Applications on this Device
- This Device Uses 128-Bit AES Encrypted Wireless Communications (Minimum) for Connection to NCD Wireless Sensors
- This Device is Equipped with a Default Wireless AES Encryption Key Common to All NCD Wireless Sensors at the Time of Shipping
- Users Have the Ability to Change the Default Wireless AES Encryption Key
- This Device Requires Physical Access to Change the Wireless AES Encryption Key
- Factory Resetting This Device will Not Alter the Wireless AES Encryption Key
- The Wireless AES Encryption Key is Stored in Protected Memory and Cannot be Accessed by our Firmware or Externally in Any Known Possible Way
- Disabling the Wireless AES Encryption Key is Not Supported by this Gateway or Sensors
- This Device Communicates to NCD Servers Upon Bootup for the Purposes of Checking for Firmware Updates ONLY
- This Device Communicates to NCD Servers Once per Day for the Purposes of Checking for Firmware Updates ONLY
- This Device Will Not Automatically Download or Install Firmware Updates
- This Device Does Not Send Access Keys, Tokens, Passwords, Encryption Keys or Any Form of Customer Data or any form of Sensor Data to NCD Servers
- Firmware Upgrades Require Physical Access to this Device that May be Initiated by Users, Installers, or NCD Engineers with Physical Access to the Device
- Firmware Upgrades Cannot be Initiated Remotely (Over the Internet)
- This Device is Configured Using a Secure WiFi Connection Connected Directly to your Computer or Smart Phone
- This Device Does Not Require an App for Configuration
- This Device Temporarily Stores Limited Sensor Data While in Configuration Mode for the Purposes of Demonstration and Configuration or Remote Sensors
- This Device Does Not Permanently Store Any Sensor Data While in Runtime (Daily Operation) Mode
- WiFi Communications is Limited to 2.4GHz
- WiFi Communications is Secured using WPA-PSK2 Security Standards during Device Configuration ONLY
- WiFi Communications is Secured by the Security Standards Defined by the Customer Router for Daily Use
- NCD Does Not Recommend the Use of This Device on a Open, Unsecured Networks
- WiFi Communications Supports the Following Security Standards for Daily Operation: OPEN, WEP, WPA_PSK, WPA2_PSK, WPA_WPA2_PSK, WPA2_ENTERPRISE
- This Device Will Store Access Keys, Tokens, and Passwords for the Purposes of Performing the Operations for which it is Intended
- This Device Supports a Hardware Reset Feature which Clears All Access Keys, Tokens, and Passwords from Memory and Erases Everything Except the Wireless AES Encryption Key
- NCD Does Have the Ability to Retrieve Access Keys, Tokens, and Passwords from this Device, but only if this Device is Physically Returned to our Office
- It is Possible for 3rd Parties to Retrieve Access Keys, Tokens, and Passwords from this Device with Extensive Programming Skills and Physical Access to this Device
- NCD is not Aware of Any Method or Process of Remotely Retrieving Access Keys, Tokens, or Passwords Without Physical Access to this Device
- Should this Device be Returned, NCD Will Not Send Any Data Extracted from this Device, Including Access Keys, Tokens, or Passwords to Any Party Under Any Circumstances
Mechanical Drawing

Wiring Diagrams
Documentation Downloads
Enterprise 868 MHz Sensors
Enterprise 900MHz Sensors
900HP-S3B Wireless Compatibility Notes
Notice: Compatibility Notes Does NOT Apply to the Following Products:
- NCD Enterprise Solutions
- NCD Wireless Sensors
- NCD Enterprise Modems and Gateways
Notice: Compatibility Notes Applies to NCD Industrial Products, Including Fusion, ProXR, ProXR Lite, Taralist, and Reactor Series Products.
Compatibility Notes
When using an 900HP-S3B communication module, it is essential that you use the ZIGMO_PCB to configure the module settings. Long-Range wireless sensors may be programmed over the air without removing the communications module.
A 900HP-S3B Modem or a gateway of some kind that support the 900HP-S3B communications module will also be required.



